Strengthen Your Cybersecurity Before Threats Disrupt Operations
Procentric Technology helps Malaysian organisations improve network visibility, secure access, manage endpoints, and simplify IT operations through trusted global cybersecurity and IT solutions.
Local IT Expertise, Trusted Global Technologies
Procentric Technology Sdn Bhd is a Malaysian IT solutions provider focused on helping organisations strengthen cybersecurity, improve endpoint visibility, and simplify IT operations.
We work with trusted global technology partners to deliver practical solutions across network access control, endpoint management, identity access management, application delivery, and data protection.
With local support and industry experience, we help organisations choose, implement, and manage technologies that fit their operational needs.
Cybersecurity & Access Control
Improve visibility, control access, and reduce risks from unmanaged or unauthorised devices.
Endpoint & IT Operations Visibility
Support IT teams with better monitoring, endpoint management, and operational oversight.
Local Consultation & Support
Work with a Malaysian team that understands local business, government, and enterprise needs.
Trusted by Malaysian organisations across government, aviation, education, media, and enterprise sectors.
Your Organisation Could Be Exposed Without Knowing It
Unmanaged devices, weak access control, and hidden security gaps can put your network at risk before an incident is detected.
Our Core Technology Solutions
We work with trusted global technology partners to help organisations strengthen cybersecurity, improve visibility, manage endpoints, and simplify IT operations.
Network Access Control (NAC)
Discover, identify, and control devices connected to your network, including managed endpoints, BYOD, IoT, and guest devices.
Identity & Access Management (IAM)
Strengthen privileged access, user control, and identity governance to reduce risks from unauthorised access.
Remote Monitoring & Management (RMM)
Monitor endpoints, manage software, support users, and streamline IT operations across cloud, on-premise, and hybrid environments.
Application Delivery
Deliver applications securely and efficiently to students, staff, labs, classrooms, and BYOD users from one consistent platform.
IT Asset Management
Track hardware, software, usage, licensing, and IT assets to improve visibility, planning, and operational control.
Data Security
Protect sensitive documents, control file access, and reduce data leakage risks with enterprise-grade data security solutions.
Why Organisations Choose Procentric Technology
We combine trusted global technologies with local expertise to help Malaysian organisations strengthen security, improve visibility, and simplify IT operations.
Local Malaysian Support
Work with a local team that understands Malaysian organisations, procurement processes, technical requirements, and support expectations.
Trusted Global Technologies
We partner with established cybersecurity and IT solution providers to deliver reliable solutions for security, visibility, and operational efficiency.
Enterprise & Government Experience
We support organisations across key sectors including government, aviation, education, media, and enterprise environments.
From Consultation to Support
From initial discussion, product demonstration, POC, proposal, deployment, and after-sales support, Procentric guides you throughout the journey.
Powered by Trusted Global Technology Partners
We work with established cybersecurity and IT solution providers to deliver practical, reliable, and scalable solutions for Malaysian organisations.
















Awards & Industry Recognition
Our technology ecosystem includes recognised cybersecurity solutions, industry awards, and certifications that support enterprise security confidence.
NAC Solution of the Year
Genians was selected to receive the Network Access Control Solution of the Year Award by Security Award Korea 2018.
View source(ISC)² ISLA Asia-Pacific Honoree
Genians’ CEO was recognised as a 2019 Showcased Honoree in the (ISC)² Information Security Leadership Awards Asia-Pacific Program.
View sourceHIWARE Awards & Certifications
NETAND / HIWARE highlights security certifications, patents, and awards including Security Award Korea 2023 Technology Innovation Award.
View sourceTrusted Across Key Malaysian Sectors
Procentric Technology has supported organisations across government, aviation, media, education, enterprise, and commercial sectors with cybersecurity and IT management solutions.
Government & Public Sector
Supporting organisations that require stronger network visibility, access control, and security governance.
Education
Helping institutions manage users, devices, applications, and IT assets across classrooms, labs, and BYOD environments.
Enterprise & Commercial
Enabling organisations to improve endpoint visibility, operational efficiency, and cybersecurity readiness.
What Organisations Gain With Procentric
We help organisations improve visibility, strengthen control, simplify IT management, and receive local support throughout the cybersecurity journey.
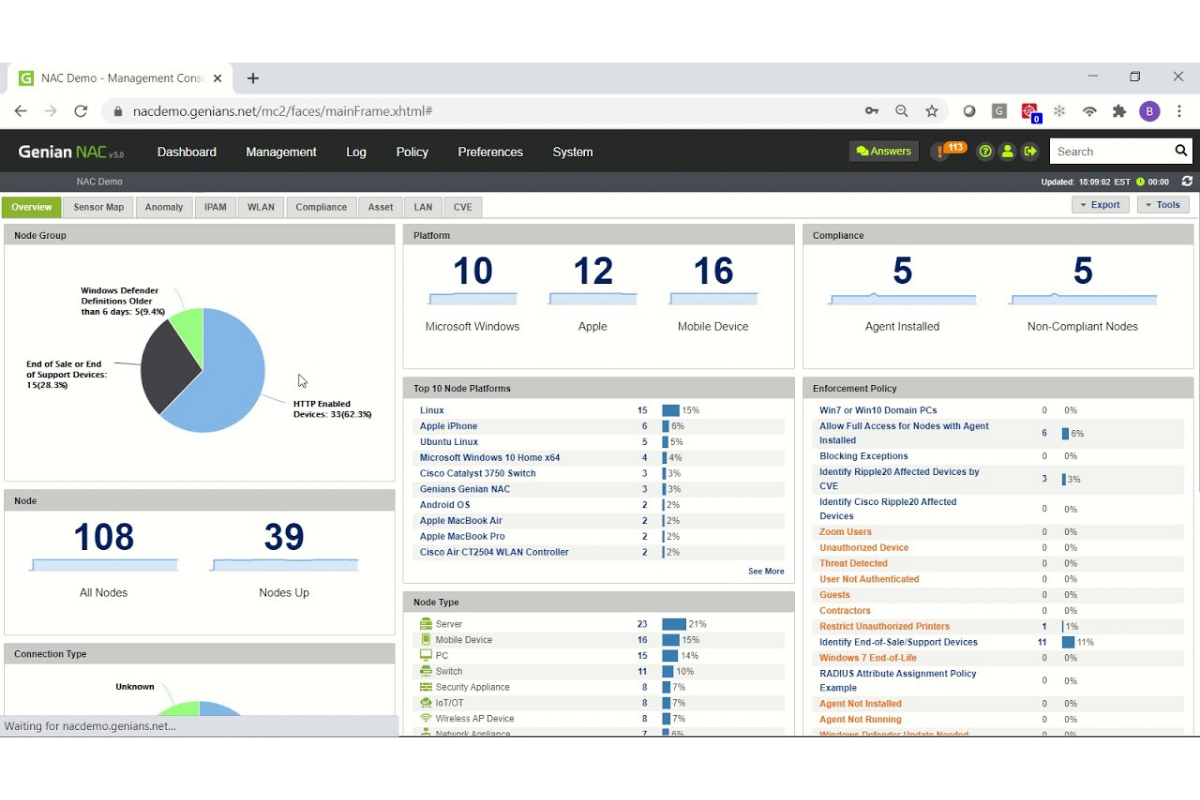
Better Network Visibility
Gain clearer visibility of connected devices, users, endpoints, and potential risks across your network environment.
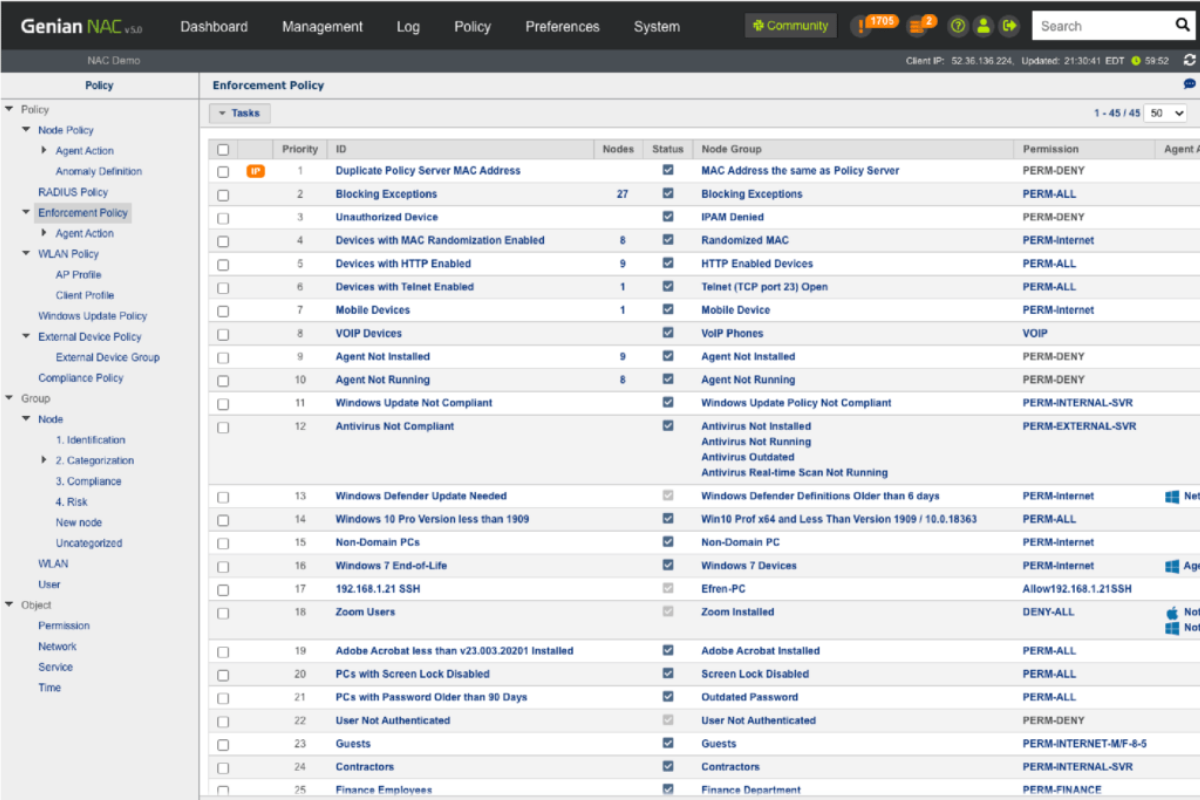
Stronger Access Control
Enforce access policies based on users, devices, compliance status, and security requirements to reduce unauthorised access risks.
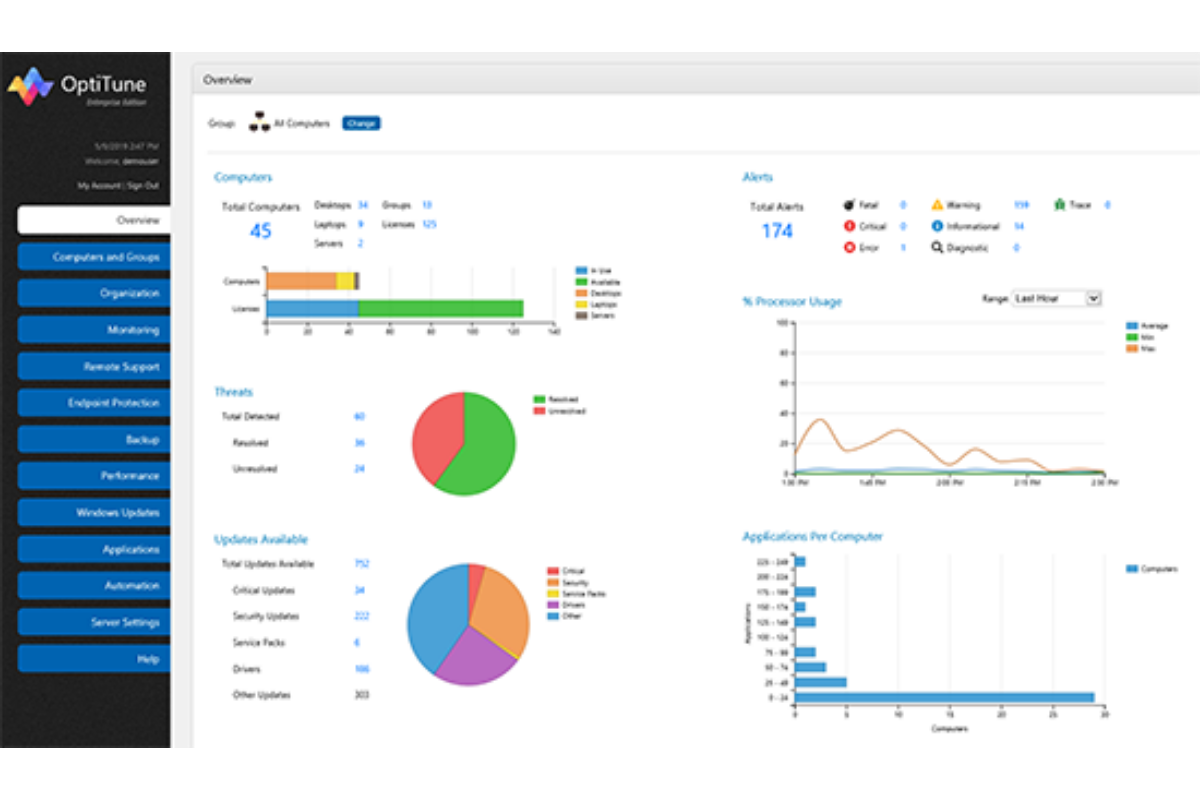
Simplified IT Asset Management
Monitor endpoints, software, updates, alerts, and IT assets from a centralised management view to simplify daily IT operations.

Local Support & Guidance
Work with a Malaysian team that supports your organisation from consultation and POC to deployment and after-sales support.
Frequently Asked Questions
Here are some common questions from organisations exploring cybersecurity and IT management solutions with Procentric Technology.
Start the Conversation
Ready to Strengthen Your Cybersecurity & IT Operations?
Share your current challenges with us. Our team will review your enquiry and guide you on the most suitable solution, demonstration, or next step.